By: Joshua Howgego
Send to a friend
The details you provide on this page will not be used to send unsolicited email, and will not be sold to a 3rd party. See privacy policy.
Last month Narendra Modi became the 15th prime minister of India since the country gained independence from Britain in 1947. But as voting took place, the press raised concerns about corruption. A piece entitled ‘How to rig the Indian elections’ highlighted how apparently easy it is to tamper with the electronic voting machines used to register votes across much of the country. [1]
One expert behind the revelations, which first came to light in 2010, was Hari Prasad of NetIndia, a cybersecurity firm. I spoke to one of his collaborators, Alex Halderman of the University of Michigan in the United States. He told me that Prasad’s private sector position was essential in carrying out the work – and that the firm's role in this area will continue to be vital.
“The problem we faced going into this work was that India didn’t really have an indigenous research community looking into election security issues,” says Halderman. “So it was just absolutely crucial to be able to have people with local knowledge of the technology community, of the political process, and access to the technology.”
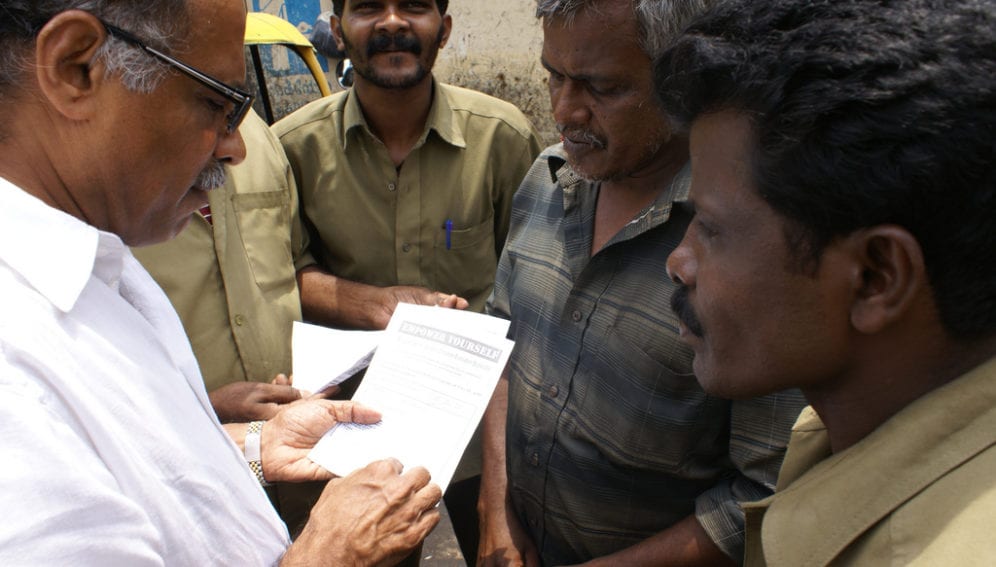
The researchers were only able to probe the weaknesses of the voting machines when a whistleblower passed Prasad an allegedly stolen machine after learning of his volunteer work on voting security. Among other frailties, they showed that hijackers could attach a fake display screen to the machines to remotely control the vote count displayed. [2]
I’m interested to know whether there is a sustainable business opportunity for the private sector in this area, but for Halderman it is important as an opportunity for the private sector to “give back” to society.
“Prasad is a smart businessman, and he knows that publicity is good. But he spent a month in jail because he refused to identify the whistleblower — so his motivation really went beyond that," says Halderman. "I think he was motivated primarily by a sense of civic duty.”
He says further academic-private research partnerships will be essential to election security in other parts of the world too. Several other countries have experimented with electronic voting systems, including in Estonia where up to a quarter of the country votes online and where Halderman has also conducted a security analysis. [3]
“In terms of developing communities within each country that are able to deal with the difficult technical details surrounding conducting elections with computers, I think it’s going to be essential to reach out to the private tech sector and try to forge new partnerships,” says Halderman. This is because there are “simply not enough” people in academia looking into the problem.
Prasad “very quickly came up to speed with the state of the art in the international research community,” says Halderman. He is probably now India’s foremost expert on election security, and has advised India’s elections commissioner on the design of a new generation of voting machines with better security, some of which were used in the recent elections.
Joshua Howgego is SciDev.Net’s deputy news and opinions editor. @jdhowgego
References
[1] Thane Richard How to rig the Indian election (Quartz, 4 May 2014)
[2] Hari Prasad and others Security analysis of India’s electronic voting machines (India EVM, accessed 11 June 2014)
[3] Alex Halderman and others Security analysis of the Estonian internet voting system (Estonia e-voting, accessed 11 June 2014)